Emil Karlsson, Aalto University, emil.karlsson@aalto.fi
In recent years, cyberattacks against industrial systems have increased significantly, and water infrastructure is no exception. Yet most of us rarely think about these systems in our daily lives, as long as clean water is available from our taps. It’s only when disruptions occur that we realize how important these systems are in our everyday lives. How can we then make these systems resilient and adaptive against evolving threats?
Resilient Water Infrastructure
Today’s water infrastructure, including treatment, distribution, and wastewater systems, needs to be able to adapt to disturbances caused by either aging physical components, system malfunctions, or cyberattacks. Especially, cyberattacks evolve and become more sophisticated, thus resilience is needed. Resilience in this context refers to the system’s ability to prevent, withstand, adapt to, and recover from disturbances within a reasonable time and cost.
Rather than focusing only on prevention, resilient systems are designed to continue operating under disturbances and to recover quickly when these disturbances occur. Although these attacks or disturbances may primarily affect only one actuator or sensor, the interconnected nature of these systems often leads to cascading effects throughout the entire process. This can complicate both the detection and recovery of the anomalies in these systems.
To address this, my research combines IEC 61499-based decentralized automation, digital twin, and artificial intelligence to explore new approaches for designing adaptive and resilient water systems. In practice, this means spending time in the lab playing with the water process system, which is presented in Photo 1. The focus of my research is the detection of disturbances and the recovery of the system to normal operation. The digital twin serves as a virtual representation of the physical water process, enabling simulation and prediction of system behavior under different conditions and actions. By comparing expected and observed system states, the digital twin can help identify anomalies and evaluate safe recovery actions before they are applied to the real system. These comparison and recovery processes are supported by suitable artificial intelligence algorithms that enable real-time analysis and decision-making.
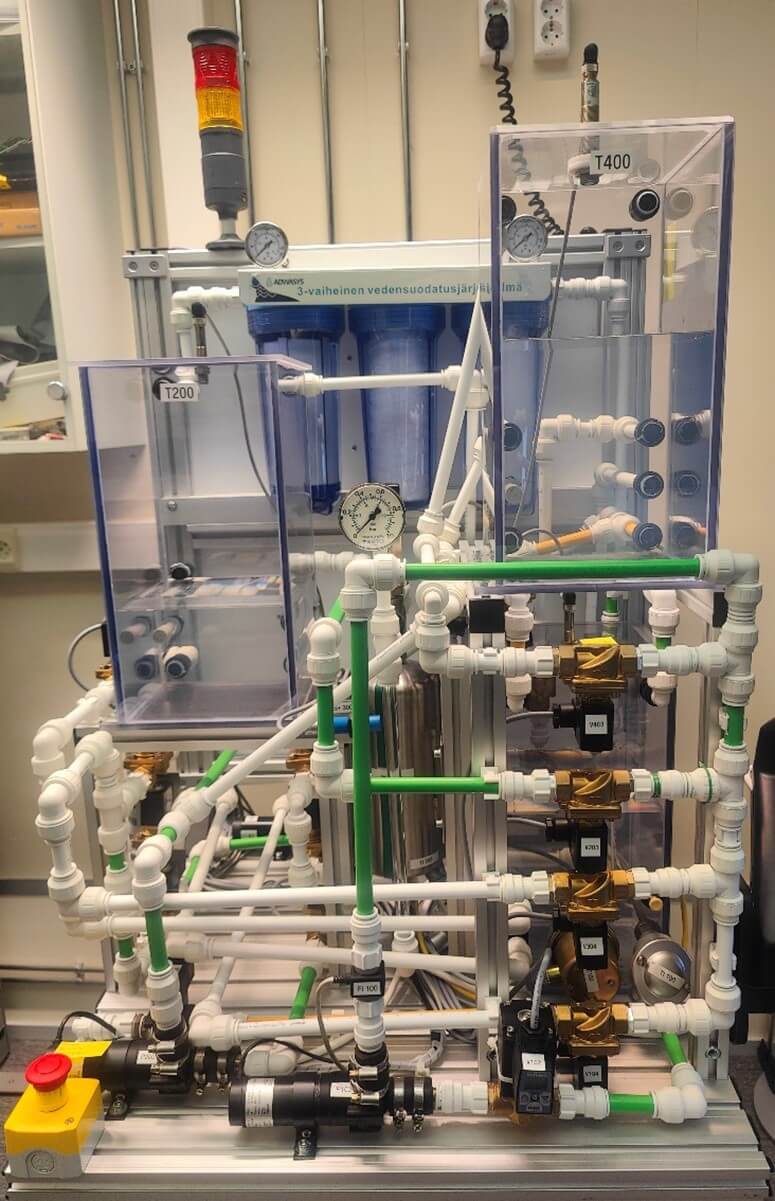
One key aspect is to test these approaches under real-time deployment while applying cyberattacks targeting different parts of the system. These can include scenarios such as falsified sensor readings, overridden actuator states, and network flooding that disrupts communication between system components. As these disturbances can create cascading effects in the system, an important aspect of recovery is identifying which data or source is compromised and which can be trusted. Otherwise, in the worst case, recovery actions may aggravate the disturbance. This real-world testing provides a better understanding of the approaches and helps us identify limitations that may not be identified using only simulations or datasets alone.
Collaboration
To transfer the research into practical and deployable solutions, collaboration with industrial partners is needed. Understanding their real-world constraints, operational challenges, and limitations helps us to guide our research toward impactful solutions. However, this journey has also shown that achieving this in practice is not always straightforward, as aligning research with industry needs can sometimes be challenging. To support the adoption, I aim to approach the problems using industrial standards and architectures, ensuring compatibility with current systems and minimizing the barriers to deployment.
As threats continue to evolve, so must our water infrastructure, where this research aims to help ensure that the systems we rely on every day remain secure, adaptive, and resilient.
30.3.2026

